NewsletterMarch 2016Newsletter Editor: In This Issue:
Meeting information
Formatting withTextEdit Do not forget to bring your used ink cartridges. Minutes of the February 17, 2016 MeetingThe February monthly meeting of MAGIC was held at the Freeland Unitarian Congregation Meeting House from 4 to 5:30 PM. There were about 40 people in attendance. In the absence of President Robert Elphick, Presentation VP Sue Keblusek , called the meeting to order at 4:00 and explained the change of format that was being tested at this meeting. In addition, a trial WiFi had been set up and people were encouraged to log in with no password. So far, it seemed to be working when the members were polled at the end of the session. The first hour was devoted was the program presented by the MAGIC Newsletter Editor, Ron Sharp, who talked about using the iCloud. Ron explained how iCloud stores data externally rather than on your computer. Below are some of the topics his presentation touched on: ADVANTAGES of using iCloud: It backs up data automatically, stores data remotely. Data can be photos, music, contacts, calendars, documents, bookmarks, keychain and mail. It syncs your data with other i-devices and allows you to share photos and access your data from anywhere on any internet-capable device, no matter what kind of computer you use. iCloud Security: All data on the Cloud is encrypted except Mail, and encryption is the same as what financial institutions use, so it is deemed to be quite secure, using a minimum of 128-bit AES encryption. In addition, you can choose to set up a two step verification with your Apple Account. With this you will get a 4 digit number texted to you that allows you to access your account. iCloud settings and options are similar between the Mac and your iDevice. You can sync automatically, by turning on iCloud Contacts . To sync photos there is an option to choose the Photo Library, all your photos, or Photo Stream, which is the last 30 days of your photo downloads. If these are on then anytime you take a photo with your iDevice the photo will automatically go to your main computer. It will store the full photo resolution into the cloud, but only put a thumbnail on your iDevice to save memory. Opening a photo will pull the full resolution image from iCloud. If you turn on iCloud Drive on then you will see iCloud on the sidebar list of folders, just as you have other folders, such as Applications, Desktop, documents, etc. BACKING UP: Turn on Backup on in the settings of your iDevice to backup your phone or iPad to iCloud. At the bottom of the settings window you can see you have 5GB of free storage. Also you can see what is using how much of your storage. You can manage your storage on your iDevice and remove some items if you need more room. Photo Sharing. If you have that set up you will see "cloud" ACTIVITY in your Photos window. The photo sharing icon looks like a little portrait silhouette inside a circle. You use the sharing icon to share any photos you choose. For photo sharing you can invite people to share with you. If you are the owner of an album you can delete any or all photos. CALENDARS: Note in the Calendar app, you can have many calendars. If you are sharing through the cloud with a family, for instance, you will see lots of calendars, so you can turn off any calendars that are unnecessary. If you set up family sharing, then purchases through iTunes may be shared with other family members. Once an item is purchased it will automatically go to everyone's account in the family sharing. ACCESSING iCloud. USUALLY it is done automatically, and you don't have to go to iCloud.com. Sign into iCloud.com on any browser. On a windows computer you can get a desktop application for that computer or a web browser. COST; you get 5GB on iCloud free. In addition you get to use for free Music, applications, books, TV shows, photo stream and photo sharing. Additional storage in the US costs $.99 per month for 50GB, $2.99 per month for 200GB, and $9.99/month for 1 TB. (i.e. most iTunes purchases are free, but if you have music from outside iTunes that is not free.) (Q about two iTunes accounts and how to marry them, you need to talk to someone. Or use senuti, that's iTunes spelled backward. That app will help make other music available.) Or iTunes Match will store all your music for $25 a year. REMOVING YOUR DATA FROM ICLOUD: Most iCloud options will ask if you want to keep your data on the device if you turn iCloud off for that app. Exceptions are iCloud Drive. FIRST drag all your information from your iCloud Drive folder before deleting or canceling iCloud, or you will lose all your data. Make sure it has all downloaded before you quit iCloud. For photo images, make sure you have the full version of the photo on your computer, ( with Photos Preferences) before deleting a photo. With Photo Streaming you can put a photo into another folder, or "import" to Photos and then it will be saved. In Photos go to Preferences, and make sure you have first downloaded all photos. Make sure images are saved on your computer before deleting them from your iDevice. OTHER STORAGE AND CLOUD DEVICES: Apple makes it easiest to use their cloud service, but you could also use drop box, google drive, amazon cloud drive,microsoft cloud or . . . We will make sure the notes are on the MAGIC website for those who didn't get a handout. BUSINESS MEETING Treasurer, Gary McIntyre, announced that as of Jan 31 we have in our bank account a balance of $6796.69 Our meeting ended with a Q and A session that was facilitated by Ron Sharp, Gary McIntyre, Sue Keblusek, Prescott and Bethany Kennedy Q: How secure do you think the Cloud is? A: Don't put stuff there that you don't want people to possibly be able to hack into it. It's up to you to decide if you want to use it. A recent news story on NPR says that even FBI can't get into these files. This makes us feel it's relatively safe. Q: What is the possibility of the Cloud losing all your data? A: An advantage with iCloud is that it syncs your data with your computer and other devices, so you always have an up to date copy. Also these big companies usually have two locations where they backup their own data. Q: My father, age 95, uses a Mac desktop and recently got a new printer. We can't get Pages to use the new printer as a default. I read in the forums that other people have had this problem as well. Each time dad wants to print something from Pages, he has to select the correct printer. A: In System Prefs you select the printer you want as the default. Also be sure you have deselected the old printer from the System Prefs Printer Window. Q: I received by email a Microsoft office document (doc file) opened it in Pages and it came in colored blue. I made changes and they came up in gold color. I tried to save the whole thing in the color black, but am unable to do so. A: We'd have to see it specifically to figure it out. Q: I can't do airdrop between my iPad and my Mac or vice versa. It's an older Mac. A: If the computer is too old then air drop won't work. Your computer needs to be around 2011 or newer for airdrop to work. Q: I'm new to Mac and went to Tom Johnson's seminar. One assignment he gave me was to attach a photo to an email. The message I was given was that there was no content in the email. But when we looked at the email the photo was there. Why did it say "no content?". A: Perhaps it was because you didn't write any text with the photo. Q: When I migrated from the old computer to the Mac my messages didn't transfer. I want to turn off iCloud on my iPhone. A: When you try to turn off iCloud it will ask you if you want to keep the data on your phone. You want to say Yes. Do NOT say you want to delete it. Q: Sometimes my son sends photos that he's taken on his iPhone, but I can't get the photo off the email and onto my desktop so I can print them. A: Double click on the photo in the email and it will open in Preview. Then print from there or use the share button on Preview to send the photo somewhere else. It could be that the photo is in a different format that the computer doesn't allow drag and drop. Q: I had trouble streaming from a radio program with my laptop. I took it to Joel who showed me that if I went from Safari to Chrome it would work. This is an old OS , that would work with Chrome, but not Safari. A: When you find a browser that won't work for you, try another browser. Sometimes they have different capabilities. Q: How can I open the ICE (In Case of Emergency) app on an iPhone when the phone is locked. (ICE is an app that contains medical emergency information for you.) A: At the bottom left corner of the number pad (where you enter your code to turn on your iPhone) is the word, "emergency." Anybody, such as a First Responder, can click on this word and the emergency App will open even without the iPhone being turned on, thus allowing helpers to get vital info on someone with an iPhone. This led to an informative discussion that everyone should know about emergency information. All iPhones have an emergency App in the shape of a heart. There are other medical emergency Apps that you can also get from the App Store. You must put your own information into this app, such as your medical problems, your prescription drugs, emergency contacts. You can also make a 911 call from this portion of an iPhone without turning it on with the four digit passcode. Bethany reminded everyone that if you make a 911 call from an iPhone you should be sure to first say what city you are calling from so that they can more easily trace your closest cell tower. Gary told about another thing everyone should do is to set up a Vial of Life, a little "medicine container" that holds vital information about you, which you keep in your refrigerator. He said you could get your doctor to sign a Physician's Directive document describing what kind of medical assistance you wish to have and what you do not want to have done. This document can also be placed into the Vial of Life. Furthermore, EMTs will also make available a sticker that you put by your entry door which indicates that you have a vial of life. Our board member Joan said that she asked how people could come to her aid if her door and windows are all locked. She was told she could get a lock box at Ace Hardware which she could code and then give that number to 911. (It is also possible to provide your entry information, such as the whereabouts of a hide-a-key to the Oak Harbor 911 center.) NOTE: I suggested that this would be an excellent and important article for our local newspapers and Bethany said she knew someone at the paper she could talk to. This could be an interesting story of how local Mac Users are preparing for their future emergencies! The meeting was adjourned at 6:00. Respectfully submitted, Penny Holland, Secretary. MAGIC MomentsFeedbackWe now have a feedback page on our website. This week a feedback came flying in so I know it works. If you want to send MAGIC feedback, suggestions, stories, experiences, or articles that you think are of interest, please go ahead and use this new form.Volunteers PleaseI am looking for a few good people to help with some easy tasks that will also increase your knowledge substantially. Tasks include:
Meetup.comMeetup.com is a new system to publicize meetings. There has been a suggestion that one of our members set up an account for MAGIC and put monthly data into it. Would you like to volunteer for this fun and easy task? If so, please Software UpdatesNote: This Software Update section of the newsletter lists the most relevant Apple updates. Not all updates are listed for all products. Additionally, I'll add other pertinent updates on occasion. Checking for Updatesby Ron Sharp, MAGIC There are no Apple updates for this month. You can check apple's website for software updates. And don't forget to update any third party software you use that isn't set to automatically update. Also, if you use Firefox browser you can update "Add-Ons" by going to the "Tools" menu and clicking the icon for checking updates. 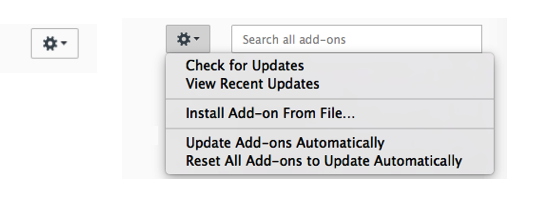
Macintosh News, Information and StoriesFind out if you've been infected by sneaky new Mac malwareby Rob LeFebvre, cultofmac.com Is your Mac infected by newly discovered malware that was ostensibly created by Milan-based HackingTeam in order to gain remote access to your machine? The new virus uses some old HackingTeam code and some new tricks to hide its tracks, but it's mostly harmless, according to researchers. That doesn't mean it's not a good idea to get it off your system. Here's how. The file — which installs a copy of HackingTeam's Remote Code Systems compromise platform — was originally reported by Pedro Vilaça, a security researcher from Sentinel One, and confirmed by Mac security expert Patrick Wardle of Synack. When initially released, the software was unable to be found by any antivirus software out there, according to Google's Virus Total detection service, though more than 40 different antivirus apps can find it now if it's on your Mac. (That list includes heavy hitters like McAfee, ClamAV and Kaspersky.) If you have one of the programs in the list above, you're good. If you don't, and want to check to see if you've gotten infected, you can check the ~/Library/Preferences/8pHbqThW/ directory. Or you can download Wardle's own antivirus program, KnockKnock, which is fairly lightweight and easy to install and use. Since the current virus uses old code from a high-profile hacking group, it's a good possibility that this is a one-off issue, created by some newer team looking for some hacker fame. Whatever the case, give the directory above a look, and/or run KnockKnock (or another antivirus app that's on the list) just to make sure. Look who's in Apple's corner in FBI privacy fightby Evan Killham, cultofmac.com 
It's raining amicus briefs in California today. Companies and organizations have filed over a dozen amicus briefs supporting Apple in its showdown with the FBI over phone encryption. Filers include law professors, rights organizations, and some of the biggest companies in the world. This outpouring of support is just the latest in a series of apparent victories for Apple in its fight to keep its devices secure. It isn't surprising that so many corporations are backing Apple here. If the courts rule that the government can compel the company to create security-compromising software, it could set a dangerous legal precedent that could also let investigators conscript other private organizations, as well. But Apple is also receiving massive support from legal professionals and political groups, which suggests that it's effectively making its case to a much wider audience. This case involves San Bernardino shooter Syed Farook's iPhone, which authorities have thus far been unable to unlock as part of their investigation. The FBI issued a warrant under the All Writs Act asking Apple to create software that will allow it to Parties that aren't directly involved in court cases can file amicus curiae ("friend of the court") briefs that support one side. They're basically a way of providing unsolicited testimony. Apple is keeping track of the briefs on its public relations site, and you can read the almost 400 pages of legal precedents and arguments, that's where you can go. If you don't, however, here's the current list of people and groups who have come out in Apple's defense:
In addition to these legal filings, Apple has also received support from the United Nations and Salihin Kondoker, whose wife died in mass shooting in December. But it's not all overwhelming support. Government lawyers in New York and Arizona believe Apple is hindering the FBI's investigation, and six of the San Bernardino victims' families filed their own amicus brief opposing Apple's position. The next hearing is scheduled for March 22. Until then, however, it looks like presiding judge Sheri Pym has a lot of reading to do. U.N. backs Apple, calls encryption fundamental to freedomby Buster Hein, cultofmac.com 
Security isn't a feature, it's a right. The United Nations is standing behind Apple in the company's fight against the FBI over whether the federal government can compel the iPhone-maker to create a backdoor into iOS. In a letter written in support of Apple's case, U.N. Special Rapporteur David Kaye says that if the feds are successful, it would infringe on citizens' right to freedom of expression. Pointing to a U.N. report he published last year, Kaye argues encryption is "fundamental to the exercise of freedom of opinion and expression in the digital age." He goes on to slam the FBI's demands as completely unnecessary. "Given that the Government has multiple, alternative technical and operational measures to conduct this investigation, it is unclear that the Government's motion to compel Apple to create software to enable access to this iPhone is necessary for this particular investigation." Kayes questions whether the FBI went to other agencies for help in unlocking the iPhone 5c that belonged to one of the San Bernardino terrorists that killed 14 people. Director James Comey told the House Judiciary Committee that the FBI had exhausted all internal resources and queried other agencies for help on unlocking the iPhone. However, some of the congressional representatives on the committee weren't convinced the FBI has tried everything. "My concern is that the subject order implicates the security, and thus the freedom of expression, of unknown but likely vast numbers of people, those who rely on secure communications," warns Kaye. "This is fundamentally a problem of technology, one where compromising security for one and only one time and purpose seems exceedingly difficult if not impossible." A number of other companies and individuals are expected to file amicus briefs in support of Apple today. The husband of San Bernardino survivor Anies Kondoker has submitted a letter in Apple's favor, arguing that there's probably not any data on the iPhone 5c in question, since it was a work phone and employees knew they could be monitored. Briefs from the ACLU, Access Now, Wickr Foundation, the App Association and more are available to view on Apple's website. Hard Drives vs. Solid-State Drivesby Ben Ryan, smalldog.com 
If you have been using computers for longer than a couple of years, it's likely that you have experienced a hard drive failure at one point or another. Hard drives are by far the most common point of failure in a computer, and here at Small Dog, we see multiple computers with failing hard drives every day. Hard drives are so failure-prone because of the way that they are built. If you imagine a record player, spinning thousands of times per second and packed into the space of a couple of inches, you have a good idea of what the inside of a hard drive looks like. Modern hard drives also have multiple disks and read/write arms stacked on top of one another, to increase storage capacity. With all of these tiny moving parts, functioning at high speed, it's easy to see why hard drives fail so often. Over time, the moving parts will just wear out until they can no longer spin or are no longer aligned correctly. Hard drives are also extremely sensitive to movement, especially sudden movement. If a hard drive is dropped or impacted, it is likely that the tiny read/write arms will scratch the surface of the disks where the precious data is stored. This can cause data to become unreadable, or the computer to stop working entirely. More and more computers are now being built with solid-state drives instead of hard drives. Solid-state drives are a newer technology that requires no moving parts at all, storing all of its information inside electronic circuits. This lack of moving parts causes solid-state drives to be much faster and more reliable than hard drives. Solid-state drives can decrease startup times to a few seconds, and are much less likely to be damaged by sudden impacts than hard drives are. The only downside to solid-state drives is the high cost per gigabyte. All new MacBooks, MacBooks Air and MacBooks Pro are built with a solid-state drive installed, starting at 128 gigabytes. I often see people confused by this, because their older computer had a much higher storage capacity than their brand new one. In most cases, the tradeoff for better speed and reliability is worth the capacity downgrade. Charge Safe with a REAL MagSafeby Ben Ryan, smalldog.com 
Most of us have had the need to buy a second MagSafe charger for our Apple laptop at some point. Maybe our old charger has worn out over the years of use, or we simply want an additional one to keep at our home or workplace. There are many different types of MagSafe chargers for sale on various websites. Many of the chargers that can be found for sale are not manufactured by Apple. These third-party chargers are typically much cheaper than the official Apple chargers, but can be dangerous to use. Third-party MagSafe chargers can shorten the life of your computer's battery, or even damage the computer by causing the battery to expand. Expanding batteries can damage the main logic board, top case, or other expensive components of the laptop. There have even been reports of third-party MagSafe adapters igniting during normal use. It is always recommended to use an official Apple MagSafe charger if one is available. You can ensure that you will receive an official charger by ordering directly from Apple or from an Apple Authorized Reseller like Small Dog Electronics. Surf Safe: A Cautionary Taleby Nathan Persing, smalldog.com 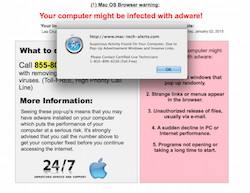
One of my first TT articles was a piece on a cold calling scam where someone would call you out of the blue and say that you have an issue with your computer and they had a fix: "Just let me remote in, install some software and for ONLY 200 dollars all of your problems are gone!" In the article I mentioned that this called a "phishing scam." Well folks today we'll talk about essentially the same scam but different rods and bait. The scammers have gotten more high tech and are taking more risks. Instead of cold calling people out of blue, they are DNS hijacking (that is a whole other can of worms) advertising servers and are then using their scripts instead of the real code. If you accidentally click on one of these pages, you will get their script using event handlers which consist of a "alert command" and a "ONLOAD command" which display a message such as: "Your Macintosh has been infected!!! Please call this number for further assistance." Now working as a technician, I have heard many times that a customer let a stranger remote in to fix a problem that didn't exist. I wondered "what is the end game here?" When one of these victims came in to make sure her computer was safe to use, she still had the number that she called handy. I decided to play the victim and call to see what happens. Before I did this, I did some prep work. First I used a fresh install of OS X with no third party software. I dd not use my home or work wifi network; I used a public one. Now I was all set up with a fresh copy of El Capitan on a MacBook Pro 2010 and phone number in hand. I dialed the 1-888 number provided and a nice person answered: "Hello, this is Rebecca. I'm with from COMPANY X. What is your issue?" I replied in a scared tone that I was surfing the web and got a pop-up on my screen that my Mac was in trouble and might you be able to help? "Sure, sir, we can help!" she responded. She instructed me to go to a website which was very primitive; just a page with three links: remote help for Windows, Mac, and Linux. The link installed a program called Team Viewer. She took control of my machine and opened System Preferences and a Terminal window and ran the netstat command, which is used for finding problems in the network and to determine the amount of traffic on the network as a performance measurement. It has NOTHING to do with malware, but she insisted that the other computers on this public wifi network were the "bad guys" trying to get into my machine. Then, in System Preferences she clicked on Security and Privacy and showed that a firewall was not installed, and she said she could transfer me to a technician and for a mere $199.99 they could fix it! At this point I decided to let her know that she was talking to a IT professional and hung up the phone. As soon as I hung up, I quickly disconnect the remote session and started to run malware scans. The scans came back clean; these scammers just wanted to scare a credit card number out of me. Don't let them fool you! If you think your computer may have a problem, give us a call instead. Also feel free to call Ron Sharp, Robert Elphick or one of MAGIC's mentors. Our info is here. Life Expectancyby Vincent Izzo, smalldog.com 
It is well known that computer have a life expectancy. When I refer to the life expectancy of a computer I'm not referring to how long it will work, I'm referring to how long you can keep it up to date with supported software and get it serviced. Many machines will work for years past their life expectancy. If you are reading this on the model pictured on the right, your machine is definitely past its normal life expectancy. There are two terms that Apple uses for machine that they no longer have hardware support: Vintage and Obsolete. Apple usually classifies a machine as vintage once it reaches 5 to 7 years past its initial release and obsolete models are those that are 7 or more years old. Apple doesn't provide hardware support for vintage and obsolete models, however most models that are vintage can support the latest software and receive updates. Once a machine becomes obsolete, however, it usually will no longer will be able to support the newest OS X and security updates. Once a machine has unsupported software the machine starts to be become more susceptible to security breaches. A common security breach comes from exploiting older software that has a known issue. Once your computer can't accept a supported OS X (which is currently 10.10 Yosemite and 10.11 El Capitan) it reaches the end of its life expectancy because the machine is no longer is repairable by Apple and the machine cannot receive software updates. Apple shuts down first-ever ransomware attack against Mac usersby Jeremy Kirk, IDG News Service via Macworld With the help of security researchers, Apple over the weekend quickly blocked a cyberattack aimed at infecting Mac users with file-encrypting malware known as ransomware. The incident is believed to be the first Apple-focused attack using ransomware, which typically targets computers running Windows. Victims of ransomware are asked to pay a fee, usually in bitcoin, to get access to the decryption key to recover their files. Security company Palo Alto Networks wrote on Sunday that it found the “KeRanger” ransomware wrapped into Transmission, which is a free Mac BitTorrent client. Transmission warned on its website that people who downloaded the 2.90 version of the client “should immediately upgrade to 2.92.” Wizard Sez: The best defence against ransomeware at this time is to keep two backups; one with Time-Machine that might be vulnerable, and one with SuperDuper or similar. If you need help with this, see this web page or call a wizard. iPhones, iPods, iPads, AppleTV and AppleWatchNew torture tests pit Galaxy S7 edge against iPhone 6s Plusby Rob LeFebvre, cultofmac Samsung's IP68 rating keeps it usable and safe underwater, but not so much when it gets dropped. In the endless battle for supremacy between Apple and Samsung, the Korean company has leaped ahead of Cupertino when it comes to water-resistance. But the iPhone 6s Plus still reigns supreme in terms of shatter-resistance. A YouTuber set the new Samsung Galaxy S7 edge next to an Apple iPhone 6s Plus in a big deep tub of water, then dropped them both from different heights, and the results are pretty predictable (yet still fun to watch). The results definitely aren't pretty.
Apple doesn't claim that any of its iPhones are waterproof, so this comes as no surprise. About 15 minutes in, the iPhone 6s Plus is wrecked and water damaged. Don't try and take that one in for a free replacement. The Galaxy S7 edge, on the other hand, is brilliantly waterproof. Samsung says the phone meets the IPX68 standard, which means it's going to stay dry in up to 3 meters of water as well as under water jet pressure. As intrepid YouTuber EverythingApplePro points out, the Galaxy S7 edge is waterproof from the inside out; when he presses on the smartphone underwater, no bubbles come out. In fact, he's able to use the phone underwater, which could be a boon to everyone who wants to take photos and video in the ocean or while skiing.
In EverythingApplePro's set of drop tests, however, the iPhone 6s Plus comes out the clear winner. The Galaxy S7 edge's backplate starts to shatter when dropped from head height. The iPhone suffers a couple of dents, but remains far more intact, even when dropped from 10 feet or higher. If your smartphone purchase is based on either waterproof rating or shatter-resistance, you now have a clear direction to go. If you're looking for a phone you can use in water, Samsung has you covered. If you want one that will take repeated drops and refuse to shatter, the iPhone is the one to get. Importance of iOS Backupsby Vincent Izzo, smalldog.com 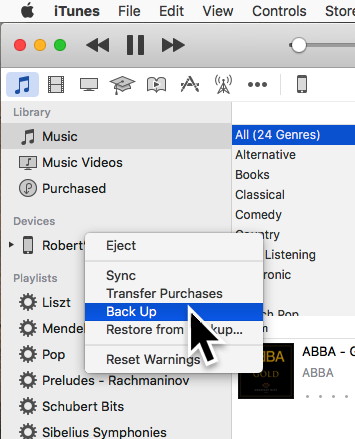
As iPhones and iPads replace notebooks and desktop Macs for users, backing up those devices become more and more important. Many iOS users have stated that they have an iCloud backup to me. Yet after having to restore their device they find out that they didn't have a complete backup. iCloud backs up a large amount of data from iOS devices but is limited to the iCloud plan the users has. Each iCloud account has 5GB of free storage and a user may purchase additional storage. The additional storage plans are $0.99 a month for 50GB, $2.99 a month for 200GB, and $9.99 a month for the 1TB plan. Even with a large iCloud storage plan, the user must set up which 3rd-party apps they are backing up. Some apps may default to backing up while others don't. You can control this by going to Settings > iCloud > Storage > Manage Storage. From this menu you can look at your current backups and see the size of your next backup. iCloud does automatic backups if and only if it is plugged into power and is in sleep mode and is connected to wifi. Another option users have is to back up their device to iTunes. All you need to do to backup your device to iTunes is plug in your iOS device to your computer running a compatible version of iTunes. Then select the iOS device icon and scroll down the page and select to backup the device using iTunes. I personally suggest using both iCloud and iTunes. I recently had a customer who lost a very important document on their iPhone. With iCloud's automatic backups it had already backed up over that document and the only way we were able to recover it was from an iTunes backup. Wizard sez: Remember that nothing is safe on any cloud! I only backup my devices onto iTunes and then back up my computer to multiple backups. How to Make Your iPhone or iPad's Text Easier to Readfrom iDrop News The default text size on your iPhone, iPad, or iPod Touch is, well, for some a breeze to navigate, and yet, for others, reading it can be a major pain in the butt — often requiring them to squint or hold the device even closer to their face in order to make out those difficult to decipher words. Fortunately, however, for those running iOS versions 7.0 or later, there are a few neat tricks you can implement to increase the size of fonts in system apps — those apps featuring Dynamic Type such as Mail, Messages, Notes, and Contacts. Here's how to make your iphone or ipad easier to read For those with an iPhone, iPad, or iPod Touch running iOS 8.0 or later, start by navigating to Settings > Display & Brightness > Text Size For those still running any version of iOS 7, go to Settings > General > Text Size. 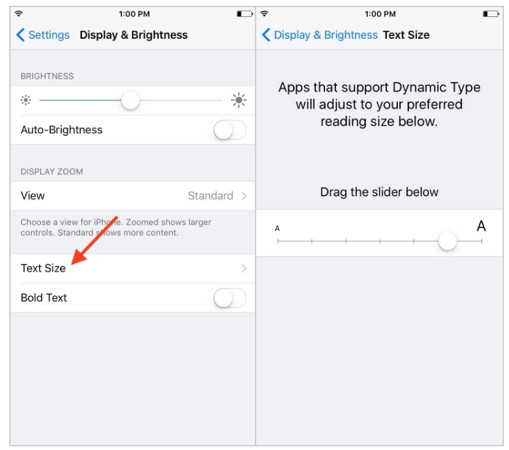
The sub-menu will display a meter, similar to the one displayed in the Twitter app, allowing you to enlarge or decrease the text size within apps supporting Dynamic Type on your device. If none of the available options on the spectrum are sufficient, however, you always have the option of making the text even larger — by switching the "Larger Accessibility Sizes" toggle to on. To do this, simply go to Settings > General > Accessibility > Finally tap on Larger Text (or Larger Type in iOS 7.) From the menu, you'll notice the Larger Text toggle we're referring to, which when activated, will enable you to increase the font size even more — like, a lot more. 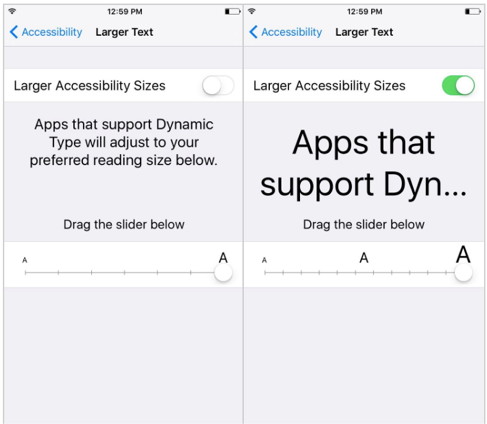
More options for better readability If the size and/or clarity still isn't sufficient for your personal needs or desires, you have two options at this point: One would be to enable the Zoom feature, located under the Accessibility settings sub-menu. Zoom can be tweaked to your personal preferences, whether they yearn for a "Full Screen Zoom" (and panning with 3 fingers) or a smaller "Window Zoom" (which will only zoom in on a particular portion of the screen — wherever the window is placed. There are a number of settings you can play around with under the zoom sub-menu, such as the zoom region, filter, and maximum zoom level — all of which can be accessed by going to Settings > General > Accessibility > and then selecting Zoom 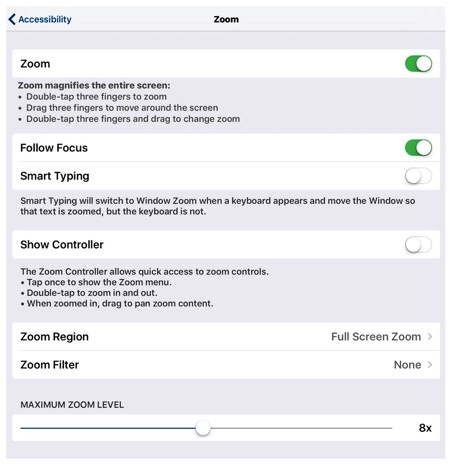
Want to increase the text clarity? You can even do that, too! Simply go to Settings > General > Accessibility. Then select the Bold Text option, switching the toggle from off to on. Be aware that enabling — or disabling — the bold text feature will require your device to reboot in order to take effect. Mac versus iPad: Why I'm on Team Bothby Jason Snell, Macworld Since the iPad Pro launched, the old debate about whether the iPad can replace the Mac as a work machine has been reignited. Jason Snell explains why he's firmly in the middle. 
We live in polarizing times: If you're not on one team, you must be on the other. Compromise is sniffed at, if not denounced outright. And yet I find myself in the middle between these two extremes. Yes, that's right: I love my Mac and my iPad and use them both. In the months since the release of the iPad Pro, the old debate about whether the iPad is a suitable replacement for the Mac to get serious work done has been re-ignited. On one side are people such as Federico Viticci of MacStories, who has almost entirely replaced his Mac with an iPad Pro. On the other are a host of skeptics who say that the iPad isn't a device suitable for real work—to get the job done, you need a Mac. This is getting silly. How to Set Up and Use Apple Pay on iPhone and Apple Watchfrom iDropNews.com Apple Pay continues to become more prevalent as a growing number of banks and retailers adopt the payment system. However, there is still a large number of iPhone users who have never setup Apple Pay. If you're looking for a complete guide describing how to use Apple Pay on iPhone or on Apple Watch then you've come to the right place. In this guide, we will walk through everything you need to know about setting up and getting started with Apple Pay on your iPhone and Apple Watch. 
Before you start Apple Pay is supported on the iPhone 6 and later and also on every version of the Apple Watch. The service is also available for iPad models with Touch ID, but only allows for in app purchases and not in store payments. If you haven't already, you need to set up Touch ID or a passcode on your iPhone. You can set this up under Settings/Touch ID & Passcode. Next, make sure that you are signed into iCloud, which you can find in Settings/iCloud. Setting up apple pay on iphone 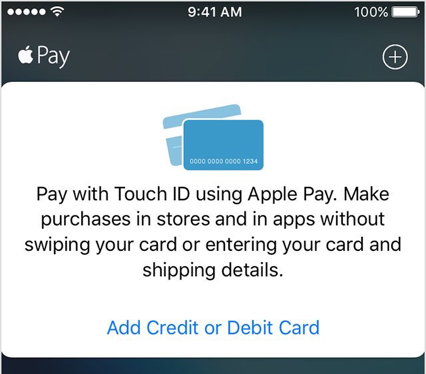
The built in Wallet app is where you will both set up and use Apple Pay. Navigate to the app and open it up to get started. Tap the option to "Add Credit or Debit Card" to setup your first card. Most major credit cards support Apple Pay, but you need to check with your bank to make sure your debit card will work with the service. If you already have a supported credit or debit card on file with iTunes, all you need to do is enter the security code on the back of the card to set it up with Apple Pay. If not, you have the option of using the camera to capture your card's information. Once you've done that, make sure everything is correct and fill in any information that is missing. Then tap next. The iPhone will go through a verification process to get your card setup. Some banks will ask for additional information to verify your card. After the verification process is through, you are ready to use Apple Pay. Setting up apple pay on apple watch If you own an Apple Watch, you can set up Apple Pay using any iPhone 5 or later. Make sure you are signed into iCloud on your iPhone. Also, on your Apple Watch a passcode must be set up and Wrist Detection turned on. Even if you have already set up cards on your iPhone, you will need to set them up again on the Apple Watch. This process is done through the Watch app on your iPhone. To add a card that is already on your iPhone, open up the Watch app and go to the My Watch tab. Select Wallet & Apple Pay and tap "Add" next to the card that you want to add. You may be asked to enter the security code. The Apple Watch will go through the same verification process as the iPhone did when you first set up your card. Once this process is over, you will get a notification on your Apple Watch that it is ready to use Apple Pay. If you would like to add a card only to your Apple Watch and not your iPhone, go through the same process as above but select "Add Credit or Debit Card" in the Wallet & Apple Pay section of the Watch app. From here the process is the same as setting a card up for you iPhone. If you have a supported card set up in iTunes, you can enter the card's security or you can use the camera to setup a new card. USING APPLE PAY IN STORESiPhone You can use Apple Pay with your iPhone or Apple Watch in any store that accepts contactless payments. Look for one of these symbols when you are checking out. 
To pay with Apple Pay using your iPhone, hold the top of your iPhone up to a contactless reader and place your finger on the Home button without pressing it. Apple Pay will activate and your default card will be used to make the purchase. If you want to pay with a different card, hold the top of your iPhone near the contactless reader without placing your finger on Touch ID. When your iPhone wakes up, tap your default card. You will then get a list of your cards and you can tap on the one you want to use. Once you've selected a card, place your finger on Touch ID and hold your iPhone near the reader to pay. To check out even quicker, you can also activate Apple Pay while your iPhone is locked by double clicking the Home button. Your default card will show up ready to use. Here, you can also tap the default card to switch cards as described above. Apple Watch 
To activate Apple Pay on your Apple Watch, double click the side button. Your default card will show up and you can simply hold your Apple Watch up to the contactless reader. To switch cards, swipe left or right. Using the Taptic engine in the Apple Watch, you will feel a tap on your wrist once the payment goes through. Using reward cards and passes with Apple Pay There are several Wallet enabled apps in the App Store which allow you to add reward cards and passes to the Wallet app. Passes are plane tickets, movie tickets, etc., while rewards cards allow you to pay or get rewards at places your regularly go. Look for this symbol inside of an app to add a card or pass to the Wallet app. 
The Starbucks app is a good example of a rewards card you can add to the Wallet app. Using the app, you can add a Starbucks card to the Wallet app which you can use to pay and earn rewards at Starbucks. Like many, the Starbucks app uses location data from your iPhone allowing the app to send a notification whenever you are close to a Starbucks. To pay, simply swipe from left to right on the notification and the card will pop up. The BoyfriendDear Tech Support, The response (that came weeks later out of the blue): Dear Desperate, 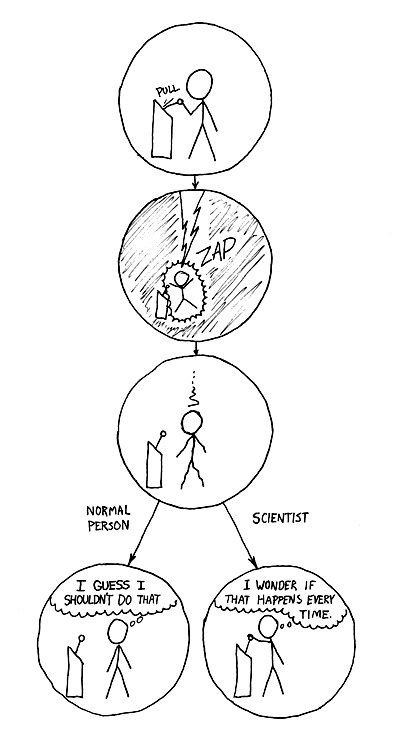 The Difference from xkcd.com Penny Holland has volunteered to be the newsletter's humor editor. We hope to tickle your funny bone on a regular basis. If you have any pictures, cartoons, or jokes that might be appropriate for this august publication, please send them to Penny at By The WayCreating a new Photos Libraryby Ron Sharp, MAGIC* There is a photo I want to show you. Wait … I have to wait for Photos app to open, takes a minute. How many photos do I have? 3000? 6000? 16000? More? Wow. It's easy to collect a large amount of photos. We snap photos and even take videos about any time now since mobile phones have offered these options with decent quality cameras. But having a huge inventory of photos makes it a bit more difficult to handle. I like to have them a little organized and labeled so I can find photos and even groups of photos easily. If you have a very large amount of pictures you can slim things down by having more than one photo library. You can separate your photos into groups by date or theme. Or if you do art you can separate all your art photography from personal or family photos. Here is a procedure for creating a new Photos Library of your specific group of photos. Note that if you use iCloud Photo Library, it will only backup one library.
First create a new folder in your Home folder. Label it so you know what to search for if you loose it; "Photos to Transfer." Then open the Photos app and gather all the photos you want to separate into a new library. You can do this by dragging them to an album in the left column that exists or that you create new. You can also do this by creating a Smart Album and use keywords. Then select all the photos in that album and export them to the folder you created, "Photos to Transfer." This will take a while if there are tons of photos to export. Now quit your Photos app. Click the Photos app icon again to open it back up but first hold the Option key. Now a window will come up that asks which Photos Library you want to open but also gives you the option to create a new Library. Choose the New Library option and give it a name. Maybe Photos Library 2, or Photos Library Art, or whatever. Then when your new Library opens it will be empty. Click on "Import" from the "File" menu and choose the photos from your "Photos to Transfer" folder. You've done it. Good job. Now that your photos are in the new library you can delete the photos from the "Photos to Transfer" folder, or just move the whole folder to the trash. When you open the Photos app it will always open the last library you had open. If you want to open the other library, quit Photos, then again hold the option key as you click to open the app. It will give you the option of which library to open. And you may have realized by now, the Photos Library is located in your Pictures folder in the Home folder. You can now open the original library and delete the photos you moved to the new library. In the Photos app, photos in the trash folder will automatically delete in 30 days, but you can delete them immediately if you are low on hard drive space. Which brings me to another point I should mention. You should check your hard drive space before starting this project. If you are very low on space, then you may not have room for making copies of a lot of photos, unless you move/export the photos to an external hard drive. This would even be preferable if you have limited hard drive space. This procedure will work with Photos app as well as iPhoto. The only drawback to having more than one Photos Library is if you use iCloud to backup your photos. iCloud will only backup the main "system" library. Other ways to make your photos more manageable is to take the small amount of time to label and sort them when you first upload them to the Photos app from you camera. Delete any that aren't good. You can also use keywords which helps to search for photos and for creating smart albums. MAGIC, the Macintosh Appreciation Group of Island County, serves people who use Macintosh computers, software and peripherals. Our goal is to share information and get answers to questions to make us more productive with our use of technology. Our monthly meetings give us a chance to discuss computer problems and share ideas with other Mac users, feature speakers on specific topics, and to keep apprised of Apple news. |